“If my thought-dreams could be seen / they’d probably put my head in a guillotine.” — Bob Dylan, “It’s Alright, Ma (I’m Only Bleeding),” 1965
The fall round of consumer-electronics tech expos in Manhattan came to an end in November, with established brand names and newbie start-ups offering the predictable (yet sometimes surprising) assortment of digital devices purporting to make your life simpler, more fulfilling, more exciting, and in every possible way better.
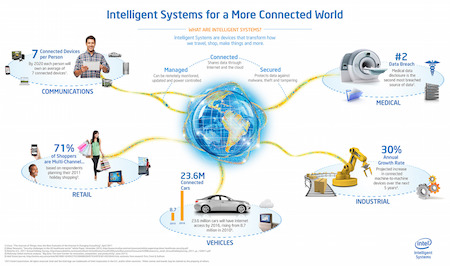
 This promise revolves around the futuristic assumption that marries the still unrealized vision of “internet everywhere” (unlimited global access to the web) to the emergent “internet of things” or IoT (everything from your car to your toaster becoming “smart” via connection to the web). All of this centered around your smartphone, a handheld, portable device notoriously subject to assorted malfunctions — moreover, one that you can easily break, misplace, or lose, and one that’s easy to steal.
This promise revolves around the futuristic assumption that marries the still unrealized vision of “internet everywhere” (unlimited global access to the web) to the emergent “internet of things” or IoT (everything from your car to your toaster becoming “smart” via connection to the web). All of this centered around your smartphone, a handheld, portable device notoriously subject to assorted malfunctions — moreover, one that you can easily break, misplace, or lose, and one that’s easy to steal.
One of the elephants in the showroom, of course, remains the inarguable unreliability of these “smart” devices and the consequent dangers they not only pose but in fact create from scratch. These have begun to get some of the attention they deserve.
•
“Pediatricians Say No to Wearable Smartphone Baby Monitors,” by Dennis Thompson, U.S. News & World Report, January 24, 2017:
“[R]epeated false alarms from the monitors jangle parents’ nerves and lead to unnecessary tests performed on babies, said Dr. Christopher Bonafide. Bonafide is a doctor with the Children’s Hospital of Philadelphia. He’s also lead author of an editorial [on this subject] in the Jan. 24 issue of the Journal of the American Medical Association (JAMA). …
“The American Academy of Pediatrics (AAP) recommends against using these high-tech baby monitors in healthy infants, said Dr. Rachel Moon, who chairs the academy’s Task Force on SIDS. …
“‘Innovation in the way we monitor kids is pretty valuable,’ Bonafide said. ‘The problem is these companies have bypassed all of the steps that exist to really protect the public from harm from these devices.'”
•
The other pachyderm in the parlor is the hackability of all these devices, which creates a much different set of risks. I introduced the issue of potential hacking of the IoT in my commentary at this blog starting with “All Geek to Me” in November 2015, expanding on it in my post “World o’ Gizmos 2016” a year later. Gratifying to see that it has become headline news:
“Be Careful Buying a Smartwatch for Your Kid,” by Michael Kan,
PC Magazine, October 18, 2017. Kan reports,
“Be careful around smartwatches designed for children. Not all are built with security in mind, according to a Norwegian consumer watchdog group.
“In tests of smartwatches sold internationally, the Norwegian Consumer Council found that three products contain security flaws, making them easy to hack. These bugs could allow a hacker to secretly spy on a child’s location, listen to voice messages, or pull name and phone number information on the device, the group said. ‘These watches have no place on a shop’s shelf, let alone on a child’s wrist,’ it added.
“The three watches tested were the Xplora, which has over 350,000 users, the Gator 2, and the Viksfjord, a product that’s been sold under different names across the world. …”
•
“The Bright-Eyed Talking Doll That Just Might Be a Spy,” by Kimiko de Freytas-Tamura, New York Times, February 17, 2017:
“Cayla is a blond, bright-eyed doll that chatters about horses and hobbies. She plays games and accurately answers questions about the world at large. She could also be eavesdropping on your child.
“That’s the stark warning parents in Germany received on Friday from the country’s telecommunications watchdog, the Federal Network Agency, which said hackers could use the doll to steal personal data by recording private conversations over an insecure Bluetooth connection. …”
This situation actually led the New York Times to issue a blunt holiday-season advisory (albeit in an op-ed piece), “Don’t Give Kids Holiday Gifts That Can Spy on Them,” by Ashley Boyd, December 8, 2017:
“This year we’re adding a new rule to our list: No toys that can spy. The idea: to keep seemingly innocuous internet-connected devices that may compromise our privacy and security out of our home and especially out of our children’s hands. …
“The consumer groups Which and Stiftung Warentest recently conducted an investigation that revealed that toys like Furby Connect and CloudPets could be hijacked by low-tech hackers. Hackers can then transmit spoken messages to kids through the toys’ speakers. …”
•
Needless to say, the problem doesn’t limit itself to items designed for kids. As the March 14, 2017 report by John Markoff in the New York Times informed us earlier this year, “It’s Possible to Hack a Phone With Sound Waves, Researchers Show.” Wired tells us that it’s possible to hack and hijack a car — while you’re driving it on the highway.
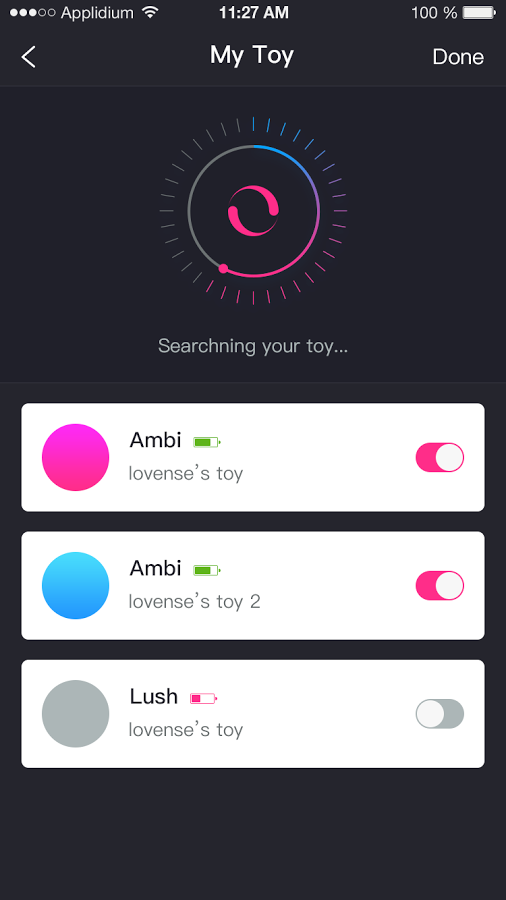
App-controlled vibrators and butt plugs from Hong Kong-based sex toy company Lovense secretly recorded user activity, which the company described as a “minor bug.” Presumably these devices were also hackable. And the bluetooth-enabled We-Vibe devices marketed by a Canadian sex-toy company “sent private data to the manufacturer through a companion app,” as a result of which Standard Innovation settled the resulting class-action suit for $3.75 million.
On the more mundane level of heat control, a cybersecurity researcher demonstrated that an app that enables the owners of Aga cookers to remotely control their high-end ovens could be hijacked by hackers. The list goes on and on. Indeed, these IoT devices don’t just expose their individual owners to malicious intrusion; their vulnerability and inadequate security enable hackers to gang them for massive attacks on the infrastructure of the web, as the Mirai botnet assault of 2016 proved.
Yet despite the mounting evidence that the IoT creates problems it can’t yet solve, Amazon wants you to let delivery people you don’t know enter your home when you’re away in order to drop off packages — even though the digital “Amazon Key” making that possible can be hacked.
Do you really want to bring into your life devices that conceivably can be made to testify against you in court? I realize that represents a remote possibility for me (and, I hope, for most if not all of my readers). But given that both black hats and white hats can demonstrably outsmart these “smart” innovations, how much control over your life do you want to cede to them? Is it really a lot of trouble to walk over to your thermostat and adjust it by hand?
•
I don’t find it onerous do so, nor to carry a wallet (with some cash, ID cards, a few credit cards) and a set of keys to my house when I step out the front door for the day. I don’t need a wristwatch to which I can talk; indeed, I haven’t worn a watch since the 1970s. I rarely need a cellphone, carrying one around mostly so my wife Anna can reach me in an emergency.
And my cellphone, as I’ve noted earlier, is by choice a basically dumb one, which is how I like it. Even so, I should add, that apparently leaves me vulnerable to spying, if I’m to believe the ease with which the CIA, the FBI, local police, and all kinds of other actors remotely track people by their phones, download their data, and turn those tools into hidden microphones and videocams in movies and TV dramas nowadays. Nor is that merely the stuff of fiction; remember that U.S. intelligence hot-miked Paul Manafort’s phone in 2016 via a remote “exploit.”
We live in parlous times, made all the more parlous by the seductive tech that entices us to betray ourselves. As a headline at Engadget put it recently, “All the cool gifts are made for spying on you. Stop surveilling yourself.” As Violet Blue writes,
We’re marinating in surveillance tech. We carry an always-on combination tracker and eavesdropping device everywhere we go (a smartphone). We agonize over picking out the best smart home microphone-speaker combination. We snarf up the latest in connected appliances. We say “yes” to all the apps, and surf the web looking for deals like it’s the pre-condom era of porn.
We know the connected devices, no matter how big the company they come from, are all bug-infested, insecure, preyed upon and riddled with shady backroom data deals. And yet.
In China they have already entered the Big Brother condition of constant surveillance. It began with the June 14, 2014, inauguration of the Social Credit System (SCS), designed “to rate the trustworthiness of its 1.3 billion citizens. The Chinese government is pitching the system as a desirable way to measure and enhance ‘trust’ nationwide and to build a culture of ‘sincerity.'” Follow-up includes a new smartphone app that allows you to “applaud president Xi Jinping for his party speech as fast as you can, and then share your results online.” (Of course, this also makes the slowness or sparseness — or total absence — of your applause evident.) Not to mention the deploying of the combination of CCTV-everywhere facial-recognition software that tracks everyone 24/7/365.
•
A few weeks ago, as I rode the IRT local from midtown Manhattan to South Ferry, a middle-aged man dropped into the seat next to mine, pointed to the paperback book in my hand, and said, “Amazing.” I happened to be halfway through a re-reading of Jacques Ellul’s 1965 classic Propaganda, which describes with remarkable precision and prescience the cultural conditions that led to the election of Donald Trump. So I assumed, with some surprise, that he referred to it because he’d read it himself.
 But my seatmate didn’t have that specific book in mind, just the fact that I held a printed book. When I looked at him quizzically, he said, “You’re reading a real book,” then waved his hand down the car. Sure enough, everyone we could see held some kind of digital device — listening to music or watching a movie, reading a digital book, playing a video game, talking on their phones or, opposable thumbs blazing, texting away.
But my seatmate didn’t have that specific book in mind, just the fact that I held a printed book. When I looked at him quizzically, he said, “You’re reading a real book,” then waved his hand down the car. Sure enough, everyone we could see held some kind of digital device — listening to music or watching a movie, reading a digital book, playing a video game, talking on their phones or, opposable thumbs blazing, texting away.
Do the world a favor this gift-giving season. Keep your thought-dreams to yourself, and encourage others to do the same. Don’t buy any digital tech, for yourself or anyone else. Think of how many “real books” you can buy for the cost of even the cheapest IoT gizmo. So use that money to buy and give books instead. You won’t regret it, and neither will those on whom you bestow that bounty.
•
 Special offer: If you want me to either continue pursuing a particular subject or give you a break and (for one post) write on a topic — my choice — other than the current main story, make a donation of $50 via the PayPal widget below, indicating your preference in a note accompanying your donation. I’ll credit you as that new post’s sponsor, and link to a website of your choosing. Include a note with your snail-mail address (or email it to me separately) for a free signed copy of my 1995 book Critical Focus!
Special offer: If you want me to either continue pursuing a particular subject or give you a break and (for one post) write on a topic — my choice — other than the current main story, make a donation of $50 via the PayPal widget below, indicating your preference in a note accompanying your donation. I’ll credit you as that new post’s sponsor, and link to a website of your choosing. Include a note with your snail-mail address (or email it to me separately) for a free signed copy of my 1995 book Critical Focus!
 But wait! There’s more! Donate now and I’ll include a copy of The Silent Strength of Liu Xia, the catalog of the 2012-13 touring exhibition of photos by the dissident Chinese photographer, artist, and poet, currently in her sixth year of extralegal house arrest in Beijing. The only publication of her photographic work, it includes all 26 images in the exhibition, plus another 14 from the same series, along with essays by Guy Sorman, Andrew Nathan, and Cui Weiping, professor at the Beijing Film Academy.
But wait! There’s more! Donate now and I’ll include a copy of The Silent Strength of Liu Xia, the catalog of the 2012-13 touring exhibition of photos by the dissident Chinese photographer, artist, and poet, currently in her sixth year of extralegal house arrest in Beijing. The only publication of her photographic work, it includes all 26 images in the exhibition, plus another 14 from the same series, along with essays by Guy Sorman, Andrew Nathan, and Cui Weiping, professor at the Beijing Film Academy.








As a techie kind of guy, I would definitely avoid an internet connected Butt plug.
I’m so unconnected with the techie world that I don’t know what a Butt plug is. But reading books has given me a good imagination.